European automotive and logistics operators face stark compliance arithmetic: NIS2 violations can result in fines of up to €10 million or 2% of global annual turnover, and national implementation timelines are actively diverging across EU member states1national implementation timelines are actively diverging across EU member states. The regulatory pressure is translating directly into capital allocation decisions on the factory floor - and the primary beneficiaries are suppliers of open-standard operational technology (OT) components.
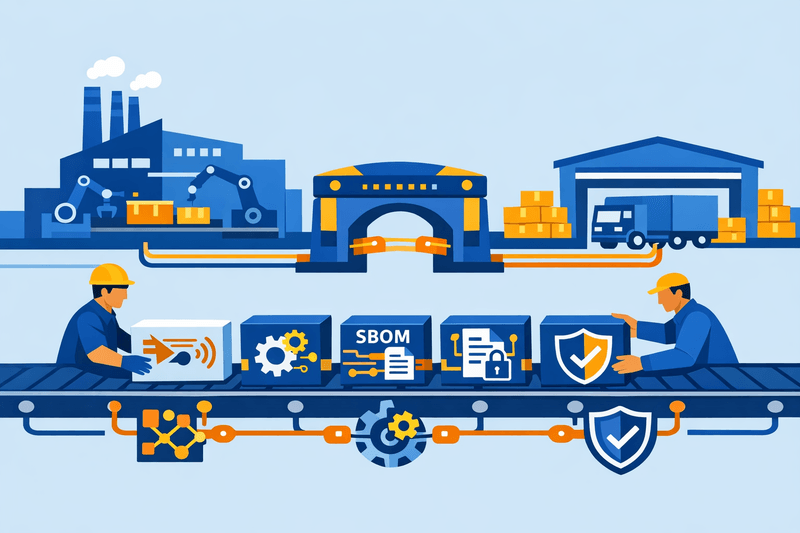
Across two of Europe's most automation-intensive sectors, a structural shift is underway. Proprietary, siloed OT stacks - once valued for performance optimization - are being reconsidered as compliance liabilities. Open-standards-based retrofit projects are emerging as the pragmatic alternative: a path that enables modular upgrades of aging controllers, drives, and human-machine interface (HMI) software without triggering wholesale OT network overhauls.
The NIS2 Pressure Point: Why Proprietary OT Is Under Scrutiny
NIS2 came into force in January 2023, with EU member states required to transpose it into national law by October 17, 2024. The directive's scope is broad, and its implications for OT operators are unambiguous: cybersecurity can no longer be treated as an IT-layer add-on2cybersecurity can no longer be treated as an IT-layer add-on. It must be embedded as a verifiable, auditable function across every connected asset in the operational environment.
For manufacturers relying on legacy proprietary OT stacks, this creates several compounding problems:
- Auditability gaps: Closed firmware architectures and vendor-specific logging formats make it difficult to generate the audit trails required for continuous compliance demonstration.
- Incident reporting bottlenecks: NIS2 requires an initial incident notification to national authorities within 24 hours, followed by a detailed report within 72 hours. Legacy OT systems built for uptime - not logging or alerting - are structurally misaligned with these timelines.
- Supply chain opacity: NIS2 explicitly makes supply chain risk management part of the security baseline, requiring manufacturers to assess every third-party hardware or software component against strict security requirements. Proprietary component ecosystems complicate this validation significantly.
- Executive accountability exposure: Under NIS2, senior management carries direct legal liability for compliance failures3senior management carries direct legal liability for compliance failures, elevating OT cybersecurity from an engineering concern to a boardroom imperative.
The implication for OT architecture decisions is direct: open, auditable stacks reduce compliance risk not just operationally, but legally and commercially.
Open Standards as the Retrofit Enabler
The retrofit wave is not driven by a single standard but by a converging set of open specifications that together address NIS2's technical expectations.
OPC UA (OPC Unified Architecture) has emerged as the de facto machine-to-machine communication protocol for NIS2-aligned OT environments. Migrating from OPC Classic (DCOM) to OPC UA eliminates a significant attack surface4Migrating from OPC Classic (DCOM) to OPC UA eliminates a significant attack surface, replacing dynamic-port, encryption-free legacy communications with a single-port, certificate-authenticated, role-based access control (RBAC)-enabled architecture. Industrial cybersecurity advisories from ENISA and BSI regularly identify DCOM as an active risk factor in OT environments.
IEC 62443 provides the technical compliance framework that NIS2 itself largely omits. NIS2 is prescriptive about outcomes but silent on implementation methods5NIS2 is prescriptive about outcomes but silent on implementation methods - it mandates what must be achieved without specifying how. IEC 62443, originally developed by the International Society of Automation (ISA) and adopted by the International Electrotechnical Commission (IEC), fills that gap with structured security levels, zone-and-conduit network segmentation models, and component certification pathways. ENISA has released updated resources mapping NIS2 obligations directly to IEC 62443 controls, providing a clear implementation pathway for OT security teams.
In practice, retrofit projects aligned with these open standards emphasize three technical pillars:
- Common data schemas for OT/IT convergence - enabling production data to flow into enterprise monitoring systems without custom integration work.
- Standardized device management APIs - supporting remote asset visibility, firmware update orchestration, and telemetry ingestion across heterogeneous equipment.
- Open security baselines - including firmware signing, verified update channels, and unified incident response playbooks that can be validated by third-party auditors and national regulators.
Sector Analysis: Automotive and Logistics Diverge in Approach
Automotive: Modular Automation Cells and Line-Side Traceability
European automotive OEMs and Tier 1 suppliers are approaching open-standards retrofits through the lens of production flexibility as much as compliance. The pressure to accommodate platform-agnostic electric vehicle architectures - combined with NIS2 supply chain requirements - is pushing line-side automation toward modular, interoperable automation cells.
The practical outcome is a redesign of how controllers, robotic interfaces, and HMI layers are integrated. Rather than hardwiring line configurations to a single vendor's control stack, manufacturers are specifying open interface requirements at the procurement stage. Controllers that support standardized communication protocols and carry IEC 62443 component certifications are displacing proprietary alternatives - not only for their security properties, but because modular configurations reduce changeover downtime and simplify audit documentation.
Traceability is a parallel driver. Open data schemas allow production events, process parameters, and security telemetry to be captured in unified records, supporting both quality management and the incident timeline reconstruction that NIS2's 72-hour detailed reporting window demands.
Logistics: Standardized Sensor-Actuator Interfaces Without Control Architecture Rewrites
Depot and warehouse operators navigate a different constraint set. Logistics OT environments - conveyor systems, automated sorting, material flow controllers - typically span large physical footprints with equipment of varying ages from multiple vendors. Full OT network overhauls are operationally disruptive and prohibitively expensive.
Open-standards retrofits in this context focus on adding standardized sensor and actuator interfaces at the edge, effectively creating a compliance-auditable layer above existing control architectures. Protocol gateways and OPC UA adapters bridge legacy fieldbus systems - Modbus TCP, Profibus - with modern telemetry pipelines, enabling asset visibility and anomaly detection without replacing the underlying control logic.
Logistics platforms that adopt standardized interfaces are also better positioned for cross-facility data sharing, a requirement as EU warehouse operators increasingly participate in federated supply chain data spaces under Manufacturing-X and similar initiatives.
Procurement Dynamics: Suppliers Are Being Sorted by Compliance Capability
The retrofit wave is reshaping supplier selection criteria in ways that carry long-term market structure implications. NIS2 requires procurement and vendor management processes to embed security standards into contracts and RFQs6NIS2 requires procurement and vendor management processes to embed security standards into contracts and RFQs, converting what was previously a technical specification into a commercial gateway requirement.
| Criterion | Proprietary OT Stack | Open-Standards OT Architecture |
|---|---|---|
| NIS2 Auditability | Difficult - closed firmware, limited logging | High - standardized audit trails, open APIs |
| Vendor Lock-in | High - single-supplier dependency | Low - interoperable, multi-vendor sourcing |
| Retrofit Complexity | High - full overhauls often required | Modular - component-level swaps with minimal downtime |
| Incident Reporting | Manual, slow log extraction | Automated via standardized telemetry channels |
| Supply Chain Validation | Opaque, difficult to certify | Certifiable via IEC 62443 and SBOM documentation |
| Procurement Leverage | Limited - lock-in constrains negotiation | Strong - competitive multi-supplier tendering |
Suppliers that can certify IEC 62443 compliance at the component level, provide documented Software Bills of Materials (SBOMs), and offer contractual security SLAs covering firmware update timelines and incident response obligations are consistently outperforming rivals whose products match them technically but cannot meet compliance documentation requirements.
Industry groups - including Plattform Industrie 4.0 and sector-specific automation consortia - are supporting this transition through reference implementations and open testbeds that allow manufacturers to validate interoperability before procurement commitment.
Retrofit Roadmap: A Phased Approach to Open-Standards Migration
Successful OT retrofit programs in NIS2-constrained environments share a common structural logic:
Phase 1 - Inventory and Gap Analysis: Conduct a full OT asset inventory, mapping each controller, drive, HMI, and sensor against NIS2 risk categories. Identify assets that lack remote management, firmware signing, or standardized communication interfaces.
Phase 2 - Define Open-Standards Target Architecture: Establish a reference architecture using OPC UA for machine-to-machine communication, IEC 62443 security levels for zone classification, and a common data schema for OT/IT data flows.
Phase 3 - Prioritize by Risk and Downtime Impact: Score retrofit candidates on cybersecurity exposure and production criticality. Schedule component swaps within planned maintenance windows to minimize operational disruption.
Phase 4 - Qualify Suppliers on Compliance Criteria: Issue RFQs that mandate IEC 62443 certification, SBOM provision, and security SLAs. Embed these requirements into framework contracts.
Phase 5 - Execute Phased Migration with Parallel Validation: Deploy replacements in staged rollouts, validating telemetry integration and incident reporting pipelines before decommissioning legacy components.
Phase 6 - Sustain Compliance Through Continuous Monitoring: Integrate upgraded assets into centralized security operations centers for real-time anomaly detection, automated compliance reporting, and audit-ready documentation.
Challenges That Could Slow Momentum
The retrofit wave faces substantive headwinds that stakeholders should not underestimate.
Legacy equipment without remote management capability is the hardest case. Some aging drives and PLCs lack the hardware interfaces needed to support any standards-based overlay - making full replacement the only viable path, at significantly higher cost and longer lead times than a modular swap.
Cybersecurity skills gaps across distributed OT environments represent a structural constraint. Large automotive and logistics facilities often span dozens of sites, each with its own maintenance team. IEC 62443 and NIS2 implementation expertise is not uniformly available at site level.
Data governance complexity increases as OT/IT convergence deepens. Common data schemas raise new questions around data ownership, cross-border data flows, and access control at the operational edge - particularly for multinational operators subject to multiple national NIS2 transpositions with varying requirements across EU member states1national implementation timelines are actively diverging across EU member states.
Stakeholders consistently identify early planning as the critical differentiator: organizations that began OT asset inventories and supplier qualification processes ahead of enforcement deadlines are positioned to execute phased migrations without production penalties. Those beginning now face compressed timelines and a supplier market where IEC 62443-certified components and qualified integrators are increasingly constrained resources.
Key Takeaways for Operations and Technology Leaders
- NIS2 compliance pressure is functionally driving preference for open-standards OT architectures over proprietary stacks, with auditability and supply chain transparency as the primary technical drivers.
- IEC 62443 and OPC UA together form the practical implementation layer that translates NIS2's outcome-based requirements into certifiable OT security controls.
- Automotive OEMs and Tier 1s are prioritizing modular automation cell designs for line-side flexibility and traceability; logistics operators are focusing on edge-layer standardization to avoid full control architecture overhauls.
- Supplier selection is increasingly gated by compliance documentation capability - IEC 62443 certification, SBOMs, and contractual security SLAs - not technical performance alone.
- Phased migration planning, early asset inventories, and data governance frameworks are the operational foundations of a sustainable retrofit program.
For a broader view of the regulatory architecture underpinning these changes, including how NIS2 intersects with the EU Cyber Resilience Act and expanded ICS/OT mandates, see the earlier analysis at EU Strengthens OT/ICS Cybersecurity under NIS2 Expansion.
Frequently Asked Questions
Which sectors face the most immediate NIS2 retrofit pressure? Automotive manufacturing and logistics/warehousing are among the most urgently affected, given their reliance on legacy PLCs, proprietary HMI stacks, and distributed OT networks. Both are classified under NIS2's scope as essential or important entities, with supply chain cybersecurity requirements cascading to OEMs, Tier 1s, and third-party integrators.
What is the relationship between NIS2 and IEC 62443? NIS2 defines regulatory outcomes - what security levels must be achieved - but is largely silent on implementation methods. IEC 62443 provides the technical engineering framework for operationalizing those outcomes in industrial control environments, covering risk assessment, network zone segmentation, component security levels, and supply chain requirements. ENISA has published explicit mappings between NIS2 obligations and IEC 62443 controls.
Can legacy PLCs be retrofitted without replacing the entire OT network? In many cases, yes. Standards-based protocol gateways and OPC UA adapters can bridge legacy fieldbus protocols - Modbus TCP, Profibus - with modern, auditable communication layers. However, the oldest equipment cohorts lacking any remote management hardware interfaces may require full replacement rather than overlay solutions.
How does NIS2 change OT supplier qualification? NIS2 formally extends cybersecurity responsibility to the supply chain, requiring contractual enforcement of security standards on every hardware and software provider. In practice, RFQs increasingly require IEC 62443 component certification, SBOM provision, and security SLAs specifying firmware patch timelines and incident response obligations.
What are the most significant risks in phased OT retrofit programs? The primary risks are legacy assets requiring full replacement rather than modular swaps, OT-specific cybersecurity skills shortages at distributed site level, and data governance complexity introduced by OT/IT convergence - particularly for multinational operators navigating multiple national NIS2 transpositions with differing local requirements.