A surge in mid-market factory retrofit projects is pushing automation vendors to align controller architectures and integration interfaces around open industrial standards, as manufacturers move to eliminate vendor lock-in and compress project timelines across operational technology (OT) layers.
Background
The pressure has been building for years. Interoperability remains a persistent challenge in manufacturing, driven primarily by proprietary protocols and communication standards among suppliers of control systems, sensors, and other devices deployed in industrial automation. For decades, the OT world has contended with proprietary systems and vendor lock-in, seeking solutions modeled on the open standards and interoperability well-established in the IT domain.
That calculus is now changing at the brownfield level. The global robotics retrofit services market was valued at USD 6.5 billion in 2024 and is projected to reach approximately USD 36.1 billion by 2034, at a compound annual growth rate of 18.6%. Control system upgrades are projected to account for 37.5% of the industrial robotics retrofit service market in 2025, driven by the critical role of modern control systems in achieving enhanced connectivity and operational efficiency. Retrofits enable legacy robots to interface with contemporary manufacturing execution systems (MES) and support real-time data analytics.
Within the broader industrial automation sector, robotics is the fastest-growing solution segment at an 11.8% CAGR through 2031. High retrofit costs at brownfield plants and rising cybersecurity risks in converged IT/OT networks remain the two most significant restraints to wider automation uptake.
Details
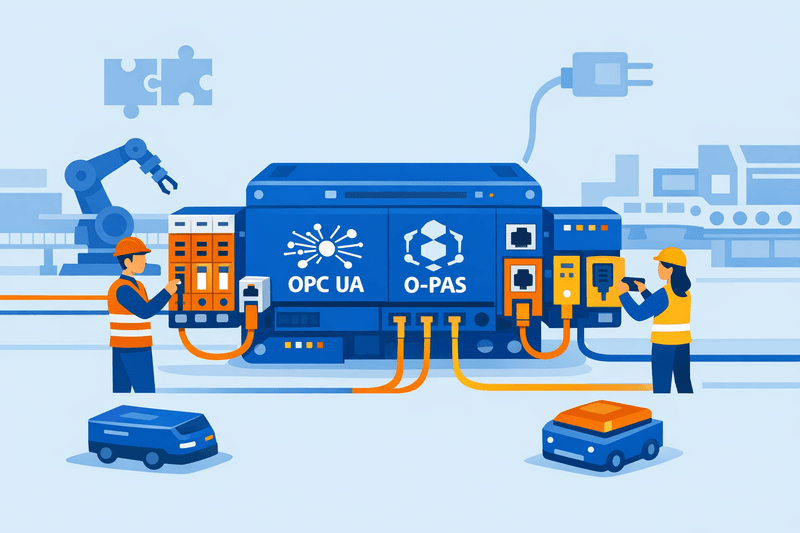
Open protocols are emerging as the practical response. OPC Unified Architecture (OPC UA) has become a widely adopted industrial standard for data modeling and secure messaging, providing a mechanism to expose machine data so higher-level systems can consume it consistently.1NIS2 in the Factory Hall: Compliance through Automation | ayedo Alongside OPC UA, protocols such as IO-Link and MQTT are increasingly cited as the building blocks of interoperable OT communication. The convergence of IT and OT is driving demand for industrial networks that support both deterministic control and IT-level data transfer, with emerging standards such as time-sensitive networking (TSN) and secure protocol variants gaining importance.
For MES and ERP integration specifically, customer demand is "clear" for open-standard solutions and greater interoperability between existing control system platforms, though full compatibility remains difficult to achieve with legacy installations-prompting new standards initiatives. Siemens has publicly acknowledged the transition. Siemens' Luis Narvaez, product manager for controllers for factory automation, stated the company is "bringing IT workflows to engineering OT devices like PLCs," introducing software development tools designed for engineers more comfortable with IT interoperability conventions. In conventional OT environments, software reuse is largely off the table, meaning companies constantly rewrite control functions for every project and at end of life-a burden that also impedes adoption of Industry 4.0 technologies such as cloud and AI-driven analytics.
Regulatory pressure is sharpening vendor accountability. The updated NIS2 Directive is now in effect, building on the 2016 NIS framework as the EU's mechanism for strengthening cybersecurity-and it directly affects OT and industrial control system (ICS) environments that serve or operate within the EU. Under NIS2, essential entities can be fined up to €10 million or 2% of global revenue, while important entities face penalties of up to €7 million or 1.4% of global revenue, with personal liability extending to senior management. NIS2 requires procurement and vendor management processes to evolve, embedding security standards into contracts and requests for quotation to turn supply chains from potential vulnerabilities into assets that strengthen resilience.
Meeting NIS2's 24/72-hour incident reporting window is practically impossible using only manual audits, given that legacy OT systems were built for availability rather than logging or real-time alerting. This is driving manufacturers to prioritize OT vendors that ship platforms compliant with IEC/ISA 62443, the global standard for securing Industrial Automation and Control Systems. Developed by the International Electrotechnical Commission in partnership with the International Society of Automation, IEC 62443 provides comprehensive guidance for asset owners, service providers, system integrators, and component manufacturers through a layered defense approach effective for securing networks, systems, and remote access channels.
Retrofitting legacy systems offers significant advantages: resolving compatibility issues with new devices and technologies, meeting current process requirements, and increasing security and regulatory compliance. The process begins with evaluating a legacy system's attributes and limitations, then integrating modern technologies to improve efficiency, streamline processes, and enhance performance and interoperability-while leveraging existing facilities to reduce costs.
Outlook
The Open Process Automation Standard (O-PAS), developed under the Open Process Automation Forum (OPAF), provides an open, standards-based, and secure architecture for hardware- and software-platform independence. Its stated value lies in reducing total cost of ownership, accelerating innovation, and increasing flexibility for industrial process control. Vendors building modular, standards-aligned platforms around frameworks such as O-PAS, OPC UA, and IEC 61499 are expected to gain an edge in mid-market bid competitions where project timelines and integration risk are primary selection criteria. As of 2025, several EU member states have published detailed NIS2 security requirements, with implementation actively underway across critical sectors. Many local authorities are introducing sector-specific interpretations that raise security maturity expectations beyond the directive's minimum baseline controls.